6 min read
"The Mother of Wi-Fi" Hedy Lamarr
In honor of Women’s History Month, we’re recognizing the groundbreaking contributions of Hedy Lamarr, a Hollywood star and tech innovator whose work...
You've likely heard the alarming statistics and the tales of cyberattacks becoming increasingly sophisticated. It's not a distant threat; it's happening right now in the digital spaces your business relies on.
Imagine, for a moment, that your data, financial security, and reputation hang in the balance. As phishing scams continue to evolve into ever more cunning and elusive forms, it's no longer a question of if, but when.
In this blog, we'll journey into the world of phishing scams, exploring their various types, the motives behind these cyberattacks, and how you can secure your email and business.
Phishing emails are tools used by cybercriminals to lure unsuspecting victims into actions that can disrupt business operations. These actions may include unauthorized fund transfers, divulging passwords, downloading malware, or disclosing sensitive data. The primary goal behind these attacks is financial gain through stealing money, data, or both.
Financial Theft: The most prevalent goal of phishing attempts is financial theft. Scammers use various tactics, such as Business Email Compromise (BEC), to execute fraudulent fund transfers or launch ransomware attacks to extort money.
Data Theft: For cybercriminals, your data is like a goldmine. It encompasses sensitive information like usernames, passwords, personal identification (e.g., social security numbers), and financial data (e.g., credit card numbers and bank account details). Once this information is in the wrong hands, it becomes a versatile tool for illegal activities. Cybercriminals may use this stolen data for financial theft, injecting malware, or selling it on the dark web for profit.
To safeguard against phishing attempts, you must remain vigilant and watch for common red flags:
Phishing attacks are constantly evolving. Scammers can target businesses of all sizes through various communication channels, including emails, texts, voice calls, and social media. Here are distinct types of phishing traps to watch out for:
In conclusion, phishing scams pose a significant threat in today's digital landscape. They are constantly evolving, adapting, and targeting businesses of all sizes through various communication channels. Understanding their motives and the many forms they take is essential for protecting your business.
While enhancing your email security is crucial, it can also be quite complex. Stay vigilant, educate your team, and consider partnering with an IT service provider like Cobb to ensure your business remains secure.

6 min read
In honor of Women’s History Month, we’re recognizing the groundbreaking contributions of Hedy Lamarr, a Hollywood star and tech innovator whose work...

5 min read
Introduction In a field historically dominated by men, Parisa Tabriz has emerged as one of cybersecurity’s most influential voices over the past...
4 min read
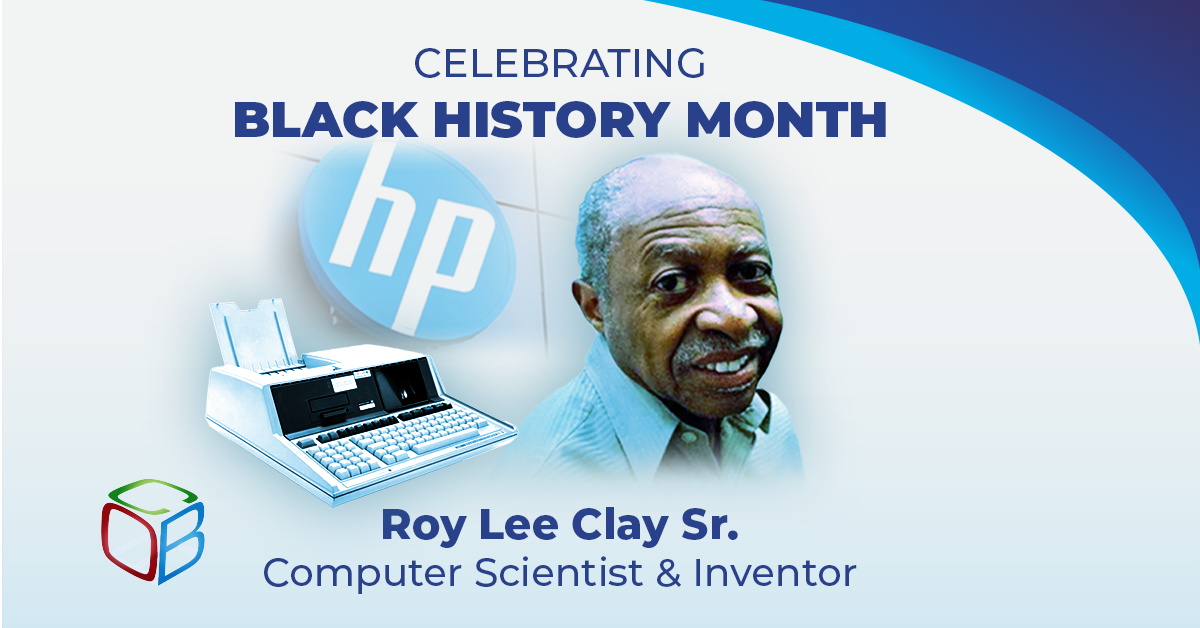
In honor of Black History Month, we want to take a moment to highlight the brilliance and innovation of Roy Lee Clay Sr, an inventor recognized for...