6 min read
"The Mother of Wi-Fi" Hedy Lamarr
In honor of Women’s History Month, we’re recognizing the groundbreaking contributions of Hedy Lamarr, a Hollywood star and tech innovator whose work...
3 min read
 Chris Wilson
Aug 7, 2020 4:17:00 PM
Chris Wilson
Aug 7, 2020 4:17:00 PM
When you own and manage a small business, you can find yourself constantly facing sales pitches. Offers to purchase memberships, software, consultants, ad space — and one group of businesses that is most definitely guilty of pushing the message of “buy, buy, buy,” is the cybersecurity industry.
There is a good reason for this push from vendors — data protection can mean the difference between your business’ success and failure. This doesn’t change one simple fact however — as a small business, it may not be in your budget to pay for expensive security packages.
Luckily, there are free solutions out there that will enhance your businesses security.
WINDOWS DEFENDER
Let’s start by going back — way back, to the founding days of the internet, and the first days of viruses. Viruses made their way onto the scene in the seventies, and truly began to propagate in the eighties. As more and more people began using the internet, viruses became more and more complex.
This complexity gave rise to different antivirus software like McAfee, Norton, Avast, and many others. And while many of these anti virus software packages worked for decades, they can now be a major hinderance to your business’ cyber security — especially free antivirus products.
Many antivirus products will now automatically come with scheduled scans turned off to persuade customers to pay for the full version of their product. This is incredibly dangerous as it can lead you to a false sense of security — believing that your business to be protected by an antivirus software, but open to attack from hackers outside of your organization.
There is a free antivirus product that has in the past few years truly began to make a reputation for itself as secure, robust, easy to use, and most importantly, easy to install and manage: Windows Defender.
This antivirus software is perfect for a small business, as it comes automatically with Windows 10, is guaranteed to work with the different tools and services you access on your network, and is automatically updated when your Windows OS experiences an update.
ARE THERE ANY DIFFERENCES BETWEEN ANTIVIRUS PRODUCTS?
Antivirus software largely functions in the same manner as any other antivirus product — the software detects viruses using two searches: active and scheduled. Active searches occur when you interact with any outside file or connection — opening and attachment in an email, for example.
Scheduled scans happen at regular intervals and will look for “tells” such as background processes using more memory than they should, minuscule changes to file data, and file extensions being changed. This last example is particularly dangerous; as Windows 10 automatically hides file extensions, users can click on a normal looking file without realizing it is actually a virus waiting to be unleashed.
All antivirus products use these tactics to scour networks for viruses, but there are advancements being made in this segment of cybersecurity. Endpoint Detection Response, referred to as EDR, is an artificial intelligence enhanced antivirus technology that relies on user patterns to predict behavior, and neutralize threats before they can even interact with your antivirus software. To learn more about EDR, read our blog, What is EDR?
Luckily, Windows Defender comes with the ability to leverage EDR technology.
OTHER FREE BUT SECURE SOLUTIONS
There are plenty of security best practices you and your employees can follow to help maintain a secure network:
Hackers will use every advantage to get into your business’ network — and this includes your own employees. Make sure your employees know what to look for when suspecting a phishing attempt — unusual email addresses, typos in the body of the email, lots of links, and above all else, calling the user to perform an immediate action. This action is usually something to the effect of “your account has been hacked — click here to change your password now.”
Once the employee has entered their password, the hackers will access their account, and change their password so the employee is locked out. From here, there is very little you can do short of a network purge of that account, causing massive amounts of lost data.
The practice of using two-factor authentication is an important way to thwart hackers. Two-factor authentication necessitates the use of two different devices to access an account. For example, in order to log in to an email account, a user will first put their password into their email client — then, a text will appear on their phone with a temporary code that will expire within a given timeframe, which the user inputs into their email client, granting them access to their account.
This prevents situations like the one mentioned above from happening — unless the hackers have access to your employees’ phone, they will not be able to access their account.
Why are backups so important? Ransomeware, a specialized type of virus, will essentially take your business’ sensitive data hostage — locking you out of your own business. Most people don’t like the idea of paying a ransom for data that they already own. If you have reliable backups you can sleep soundly knowing that an attack won’t require a ground-up rebuild of your environment.
Backups will, however, ensure this is a nonissue. With proper backup storage, you can simply repopulate your data using the backup server after cleaning your regular server of the ransomware.
For more on backups, read our blog, Backups: What Your Business Needs to Know.
If you are a small business owner, do yourself a favor, and make sure your Windows Defender is installed and updated, and that your employees know the dangers hackers present to your business. And always remember — the cost of partnering with a managed IT service provider may be less than you think.

6 min read
In honor of Women’s History Month, we’re recognizing the groundbreaking contributions of Hedy Lamarr, a Hollywood star and tech innovator whose work...

5 min read
Introduction In a field historically dominated by men, Parisa Tabriz has emerged as one of cybersecurity’s most influential voices over the past...
4 min read
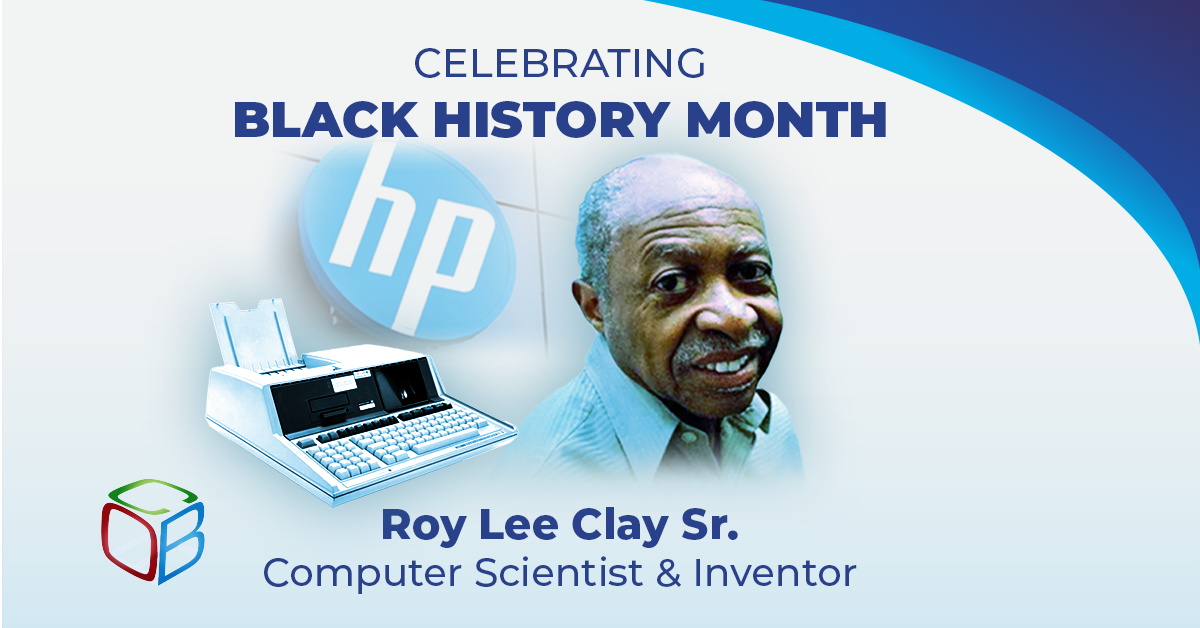
In honor of Black History Month, we want to take a moment to highlight the brilliance and innovation of Roy Lee Clay Sr, an inventor recognized for...