6 min read
"The Mother of Wi-Fi" Hedy Lamarr
In honor of Women’s History Month, we’re recognizing the groundbreaking contributions of Hedy Lamarr, a Hollywood star and tech innovator whose work...

By now, it seems as if the majority of the whole world is working from home. And while that does bestow us with the opportunity to get away with wearing pajama pants during meetings held in our impromptu office spaces, it also gives hackers the opportunity to steal vast swathes of sensitive data through un-secured home networks.
So, how do you secure your home’s network?
USE A VPN
Through the use of a Virtual Private Network, not only will you be able to access your business’ server, you’ll be able to do so securely. This means that all of your essential files, projects, and applications will be available to you, without having to copy them onto your device’s hard drive.
What a VPN actually does is provide a secure connection from your device, to your business’ network — therefore extending a private network (your business’ server) across a public network (your internet connection). Because of this, you never want to enable a VPN on your personal laptop or PC — which is essentially the same thing as bringing in your personal device and directly plugging into your office’s network.
If you connect with an un-secured device, you create backdoor access for malware to infect your network. When using a VPN, only use a trusted device — a device supplied by your company, with proper anti-virus software and firewalls, in order to protect your data and connection between your personal wi-fi and your business’ network.
IF YOU CAN’T USE A VPN, USE KVM SOFTWARE
Keyboard, Video, and Mouse software such as LogMeIn, Symless, and Multiplicity can provide an alternative if you’re in a work-from-home situation without a trusted device. Rather than connecting to your network, KVM software turns your personal device into a remote control for your work device.
This means that even if your work device is unable to go home with you, you can still use it to perform your everyday tasks as if you were there. Once you’ve connected to your work device with your KVM software, you’ll have control of that device’s keyboard and mouse, and your screen will show what your work computer is seeing in a window presented on your personal device.
It’s like a widow to your work computer, that you can reach through and interact with things on the other side. Through this connection, you’ll be able to access your company’s network like usual. And because it’s only KVM data that is being passed through the connection, you won’t have to worry about data being stolen in transit.
WORK FROM HOME SECURITY BEST PRACTICES
If you do bring a trusted device home with you, you’ll want to make sure to encrypt your hard drive. If your device is stolen or goes missing, anyone can extract the hard drive, plug it into a new machine, and read the data off of it — unless it’s encrypted. It’s always a good idea to encrypt your work device’s hard drive in any situation, but especially important when working from home.
It’s also a good idea to begin changing your wi-fi’s password regularly, and making sure the password is complex — using numbers, symbols, and case sensitive letters. Anyone who has connected to your wi-fi in the past will have access to the data that is passing through your VPN if they have access to your wi-fi.
You’ll want to begin treating your home network like your business’. While this doesn’t mean you have to forgo the use of social media, YouTube, Netflix, and other forms of online entertainment, you’ll want to make sure you’re not opening your network to any security risks. Sites that don’t have HTTPS connections, disreputable sites, and any links in emails from contacts you don’t know should be treated as if they are potential security risks.
If you can afford to do so, and you’ll be working from home for a time period long enough to warrant it, you may want to consider creating a second network at your home. This is a simple, but time consuming and relatively expensive task — all you need is a second router that is only used for business purposes. While much more secure than a regular home network, the expense and time frame may not be doable.
PRACTICE SOCIAL DISTANCING WITH YOUR HOME NETWORK
While working from home, it’s best to stay away from devices and sites you don’t trust — just like how we’re all staying away from social gatherings and avoiding highly-trafficked areas. Make sure you’re never connecting directly to your network without the use of a VPN, or by using KVM software. Just like COVID-19, precaution might seem like more trouble than it’s worth — but an abundance of caution is your best defense against viruses — both digital and real.

6 min read
In honor of Women’s History Month, we’re recognizing the groundbreaking contributions of Hedy Lamarr, a Hollywood star and tech innovator whose work...

5 min read
Introduction In a field historically dominated by men, Parisa Tabriz has emerged as one of cybersecurity’s most influential voices over the past...
4 min read
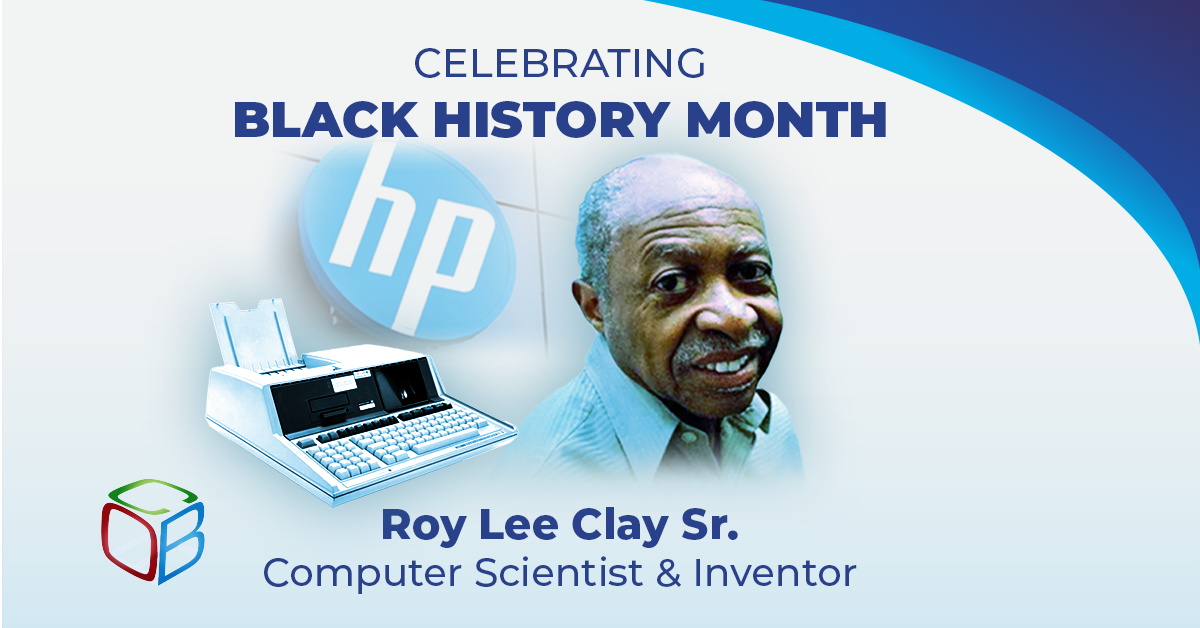
In honor of Black History Month, we want to take a moment to highlight the brilliance and innovation of Roy Lee Clay Sr, an inventor recognized for...