6 min read
"The Mother of Wi-Fi" Hedy Lamarr
In honor of Women’s History Month, we’re recognizing the groundbreaking contributions of Hedy Lamarr, a Hollywood star and tech innovator whose work...
3 min read
 Cathy Miles
Sep 21, 2023 1:21:26 PM
Cathy Miles
Sep 21, 2023 1:21:26 PM

In today's world, where every device is a potential gateway for cyberattacks, it is crucial to prioritize network security by safeguarding your office equipment.
Often overlooked, printers are no exception to this. And, when it comes to printer security, HP offers a comprehensive suite of security features designed to protect your device and data right out of the box.
As soon as you plug in your printer and connect it to your network, HP starts protecting and securing your device and the data and documents it handles.
Imagine a scenario where a hacker gains access to your office's network through an unprotected printer. They could intercept sensitive documents, compromise data integrity, or launch attacks on your infrastructure.
To prevent such incidents, HP has implemented four major features to fortify its printers against these threats.
HP Sure Start is a security feature that guards your printer's BIOS (Basic Input/Output System). The BIOS is a program that helps to initialize hardware operations and manage the data flow to and from the operating system at the time of bootup.
Just as your laptop or PC boots up and begins its security protocols, your HP printer does the same with HP Sure Start. This feature ensures that whenever your printer powers on, it starts with a clean copy of its BIOS to prevent and eliminate any potential hacking attempts or anomalies. This proactive measure ensures that your printer starts in a clean, secure state every time.
Whitelisting is a security strategy that permits only authorized software to run on your printer. This feature uses code-signing to make sure that only known HP firmware versions are loaded, working to minimize the risk of malware infiltrating your device.
While it's common practice to prevent unauthorized software installations on devices, adding whitelisting to the list of HP’s security features helps to ensure your printers are protected from every angle.
HP's Connection Inspector monitors outbound network communications from your printer, such as a fax or scan to email. It searches through connections to detect anomalous activity, flagging any attempts to breach your network.
Essentially, this feature scans for any instances where a network intrusion might involve a bot pinging unfamiliar sites, such as somewhere in New Zealand or Russia, as is common with hackers when they compromise a network.
Once an anomaly is detected, HP's self-healing mechanism springs into action, immediately notifying your IT team and shutting down the printer. Your device will then reboot to a clean state or remain shut down, depending on how you choose to program it. This process keeps your business one step ahead of any malware attacks.
Runtime Intrusion goes beyond basic protection by scanning the print stream for anomalies, especially when printing files from external sources. This feature detects anomalies in the system memory and protects the printer while it is connected to the network.
For instance, if an HR department prints a resume with embedded malware, HP detects and prevents the malware from infecting your network. HP's self-healing feature then quickly cancels pending print jobs, eliminates the malware, and reboots to return the printer to a secure state.
Memory Shield: HP adds an extra layer of security with Memory Shield, encompassing protection not only for printing but also for faxing and scanning.
HP's Memory Shield follows a Zero Trust model, which assumes no device or connection is trusted by default. Instead of relying on a traditional network perimeter to protect your resources, a zero-trust approach verifies every connection and request before granting access.
With Runtime Intrusion and Memory Shield, your device is constantly looking for new anomalies without the need for firmware updates. These features work to prevent unauthorized access to your device and curb security breaches.
For large organizations with complex compliance requirements, HP offers the Print Security Manager. This policy-based solution simplifies your device management by establishing policies, automating fixes, and maintaining ongoing compliance across your printing fleet.
Print Security Manager allows businesses to scale out their security best practices, ensuring compliance with industry standards and policies. By seamlessly pushing policies to all devices, businesses can streamline their IT management.
In today's interconnected world, printers are considered endpoint devices, making them potential targets for cyber attacks. Yet, printers are often overlooked in cybersecurity discussions, causing them to be highly vulnerable due to a lack of effective protective measures in place.
In the unfortunate event of a security breach, the costs can be staggering. Beyond potential financial losses, a breach can damage your reputation and erode customer trust. With HP's security features, you're not just safeguarding your printers; you're protecting your business from the consequences of a potential breach.
Whether you run a large organization or a small business, HP's commitment to printer security provides advantages. With features like Sure Start, Whitelisting, Runtime Intrusion Detection, and Connection Inspector, you can ensure your printers are well-protected right out of the box.

6 min read
In honor of Women’s History Month, we’re recognizing the groundbreaking contributions of Hedy Lamarr, a Hollywood star and tech innovator whose work...

5 min read
Introduction In a field historically dominated by men, Parisa Tabriz has emerged as one of cybersecurity’s most influential voices over the past...
4 min read
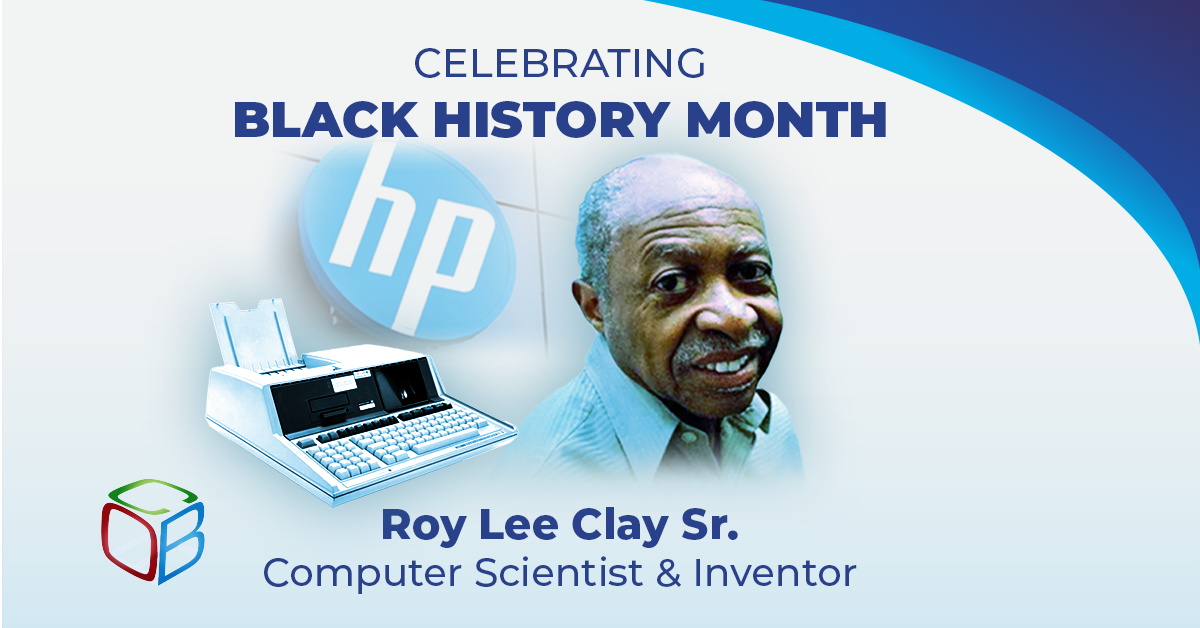
In honor of Black History Month, we want to take a moment to highlight the brilliance and innovation of Roy Lee Clay Sr, an inventor recognized for...