6 min read
"The Mother of Wi-Fi" Hedy Lamarr
In honor of Women’s History Month, we’re recognizing the groundbreaking contributions of Hedy Lamarr, a Hollywood star and tech innovator whose work...

Q4 started two months ago. While we all take a moment to let that sink in, let’s take a step back and be thankful that we all made it through this year without suffering any breaches in our networks. Or, if you did, it was shallow enough for your business to recover.
Cybersecurity is a buzzword-y buzzword by this point, and by now, we’re all probably very tired of hearing about it. Our opinions on the matter, however, don’t change the situation.
Bad actors, cyber criminals, hackers — whatever you call them — are going to invent new ways to steal your business’ data in 2023. Do you have a plan to evolve with a digital landscape that is constantly witnessing more frequent and more successful cyber attacks?
If you don’t, it’s not the end of the world. There are a lot of preparations you can do, right now, for free, to protect your business’ network from outside intrusion. There’s also a lot that unfortunately can’t be done for free, nor by yourself. However, gone is the need for employing a team of IT and cybersecurity experts through your payroll — managed service providers and cloud services have seen to that.
One of the best ways to protect your network is to make sure the devices it comprises are all up to date. However, this doesn’t just mean your employee’s laptops or desktops: it includes any smartphones, printers, routers, or servers on your network as well. Essentially, if it connects to the internet, it can and should be updated regularly.
Think you’re done updating? Think again. Check all of the different applications your employees use on their workstations: Salesforce, Quickbooks, your preferred ERP… just like devices, applications must be regularly updated.
Finally, any devices like your office copier will use firmware as their layer of security — and just like the operating systems on your devices, and the applications that run on them, your firmware must be up to date to provide you with the maximum amount of security possible.
There’s another thing you can do right now for free that will increase your security: change your password. If you’d like to check to see how effective your password is, use our password checker tool.
Cybercrime is constantly evolving — it has to. Once a vulnerability is made public, there is a small window of time for bad actors to take advantage of the vulnerability before patches are released and best practices are updated to defend against it.
It’s a two-way street, however. Cybersecurity professionals must react to the evolving tactics of cybercriminals. Because of this, it’s important to be aware of what has changed, what new threats are on the horizon, and what new technologies are being released to combat them.
A.I.
Artificial Intelligence is a double-edged sword. Both cybersecurity professionals and bad actors can use the power of AI to their advantage. AI is now being deployed in applications like Endpoint Detection and Response (EDR) software, which allows for quick analysis of security events, and quick responses without necessitating human intervention.
On the other hand, deep fake AI technology is already causing headaches for cybersecurity professionals. When anyone can use this technology to impersonate anyone else, plus the plentiful opportunities for visual spoofing made possible via remote work and virtual meetings, deep faking could possibly become the problem to look out for.
Global Events
We are all acutely aware of the instability rocking the worldwide economy, geopolitical climate, supply chain, manufacturing, food production… I’d keep going, but this list is getting to be a bit long.
Global events like the pandemic don’t just interrupt your workflows — they necessitate quick and sweeping organizational changes. When the pandemic first hit, how long did it take your office to have every remote employee working through a secure VPN connection while at home?
When fast changes are forced on an organization, it’s easy to leave cracks in your organization’s security framework. The more global events that interrupt your organization’s day-to-day flow, the more opportunities bad actors have to break into your systems.
Cloud Security
The cloud has been the greatest advancement in cybersecurity since https was invented. There are so many applications for using cloud services to increase your organization’s level of cybersecurity.
Cloud services are generally much more secure than a local server, due to extremely high levels of security measures put in place to keep clients’ data safe.
It’s due to this decentralized, highly secure nature that cloud providers have become the number one protection against ransomware. If your backups are located in the cloud, it doesn’t matter if your local environment is encrypted and you are unable to access your data.
With cloud backups, you can simply purge your local system, check to make sure all traces of the ransomware are gone, and then download your backups from the cloud. Just make sure your RTO and RPO are set up to ensure you can quickly spin up backups that reflect a recent snapshot of your network.
IoT
Your smart fridge ordering groceries on your behalf is fantastic. Your smart mirror displaying the weather forecast while you brush your teeth is pretty cool. But all of these devices with internet connections increases the number of attack surfaces available to bad actors.
An attack surface is anything a cybercriminal can use to gain a foothold into your network. And unlike laptops, desktops, and smartphones, IoT devices like your robot vacuum cleaner aren’t all that secure in comparison.
By 2027, experts estimate there will be about 64 billion IoT devices deployed on the market. That is a lot of attack surfaces.
Mobile
You’re probably not surprised to see “mobile” listed here, and for good reason too. More than half of all users on the internet engage with websites via mobile devices. While incredibly handy, smartphones have one glaring flaw: they are carried with us everywhere we go.
This opens up your phone to a much wider array of attacks. If, for example, you connect to the public network at a cafe, any other device that is connected to that network has the ability to locate your device on the network.
If a bad actor is using one of those devices, they can infect your phone with malware or ransomware. From that point, they’ll wait for your phone to connect to another network, and see how valuable the new network is, in terms of potential for a data ransom. Ultimately, the reason mobile devices are listed here is for the same reason IoT devices are — a phone is just another attack surface.
Supply Chain
While this is a problem that encompasses pretty much every human-made system in the world, the global supply chain is a valuable target for ransomware attacks.
Supply chains, by their very nature, are comprised of a multitude of devices — from GPS and POS systems, to smartphones, servers, and satellites. As mentioned above, cybersecurity experts refer to these as attack surfaces — meaning your supply chain, to a bad actor, is just a million different opportunities to steal your data.
Once your supply chain has experienced a cyberattack, it can cause two problems: the chances of your organization’s data being stolen skyrockets, and your ability to meet customer expectations dwindles as your supply chain experiences delays and interruptions.
It can be very difficult to manage the security of your supply chain, especially when you’re partnered with businesses and entities from outside your organization. The best thing that you can do is to prepare by shoring up your own network as much as possible, and having a backup plan for when your supply chain experiences delays.
Ransomware
We’ve mentioned it throughout this blog plenty enough already, but ransomware is worth covering in depth.
Ransomware is used by bad actors to lock you out of your business and customer data, and then demand a payment from your business in order to access the stolen data. This is done through malicious encrypting.
A bad actor, after breaking into a network, will either begin snooping around your network, or sell the network access to another cyber criminal. On average, cyber criminals spend 23 days in your network before taking any action, using this time to familiarize themselves with your network’s functionality, systems, and user permissions.
After finding all of the valuable elements of your network, the bad actor will begin to encrypt your network’s data, using a key to which only they have access. This can happen at any time: on a Friday evening, during your office’s lunch hour, or at the end of the day.
This is why, as mentioned above, backups are your best defense against ransomware — if you do fall victim to a ransomware attack, you can simply delete your current network, and restore it to a healthy state. Just make sure your backed-up data is ransomware-free before bringing your backups onto your network.
Automotive Hacking
Just like a smart fridge, newly-manufactured automobiles are IoT enabled devices. Cars now use programs and AI to assist with driving, managing systems within the automobile, and communicating with GPS systems.
This makes automobiles a high priority target for bad actors targeting specific individuals. Due to all of the digital, real-time systems enabled in vehicles today, cybercriminals can pull location data, form a detailed list of your habits and regularly-scheduled meetings and outings, and even listen in on conversations that take place in your car, by listening through your car’s bluetooth microphone.
Phishing
We couldn’t write a blog about cybersecurity in 2023 without mentioning phishing. Phishing is still the number one method for initially breaking into personal and business networks. This is because of human error.
Phishing is the vehicle ransomware and other nasty viruses ride in on, by using the fallibility of your employees against the defenses of your network. Once an employee has fallen victim to a phishing scam, the employee’s account will be used against your system, and unless caught, will eventually lead to a full-blown attack on your network.
This is why many businesses today employ security awareness training services, which train your employees on how to spot a phishing attempt, in order to reduce their chances of falling victim to one.
Your business’ network may be a high value target for bad actors, but there’s a lot of different cybersecurity options available for you to choose from. To learn more about what tools, partnerships, and services you can use to increase your network’s defenses, visit our blog, What is SOC as a Service?

6 min read
In honor of Women’s History Month, we’re recognizing the groundbreaking contributions of Hedy Lamarr, a Hollywood star and tech innovator whose work...

5 min read
Introduction In a field historically dominated by men, Parisa Tabriz has emerged as one of cybersecurity’s most influential voices over the past...
4 min read
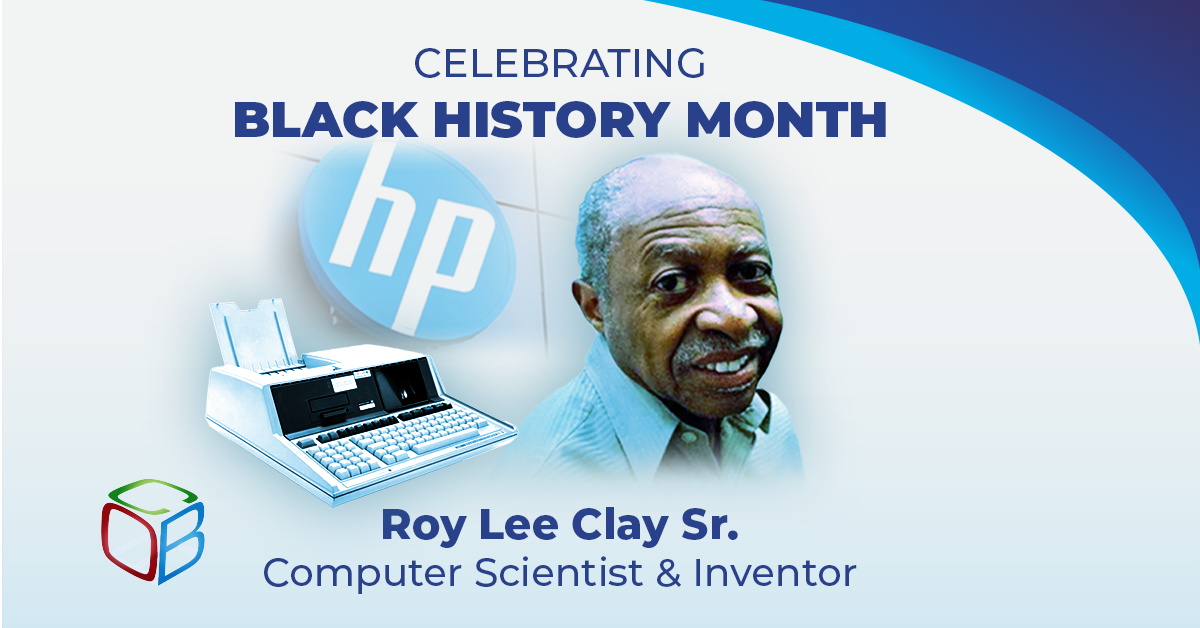
In honor of Black History Month, we want to take a moment to highlight the brilliance and innovation of Roy Lee Clay Sr, an inventor recognized for...