9 min read
Sustainable Printing: The Impact of ENERGY STAR Imaging Equipment
Sustainability has become a top priority for businesses looking to minimize their environmental impact while maximizing efficiency. Yet, as...
3 min read
-1.png) Geri Hodnett
:
Jul 24, 2018 12:21:48 PM
Geri Hodnett
:
Jul 24, 2018 12:21:48 PM
Following their breakout first edition, director Lance Acord and HP's amazing series, "The Wolf," continues with this stellar second installment. This time, our cyber villain Christian Slater breaks into a healthcare network:
Okay, so the scenario of hacking into a doctor's office network to basically poison a Chief Information Security Officer might be a bit far-fetched at first. But, consider this - healthcare is consistently ranked in the top five (if not number one) of most cyber-attacked industries. When there is a spotlight of criminal activity highlighting every corner of the industry, the most absurd/least prepared for scenario is usually the one that will let them in.
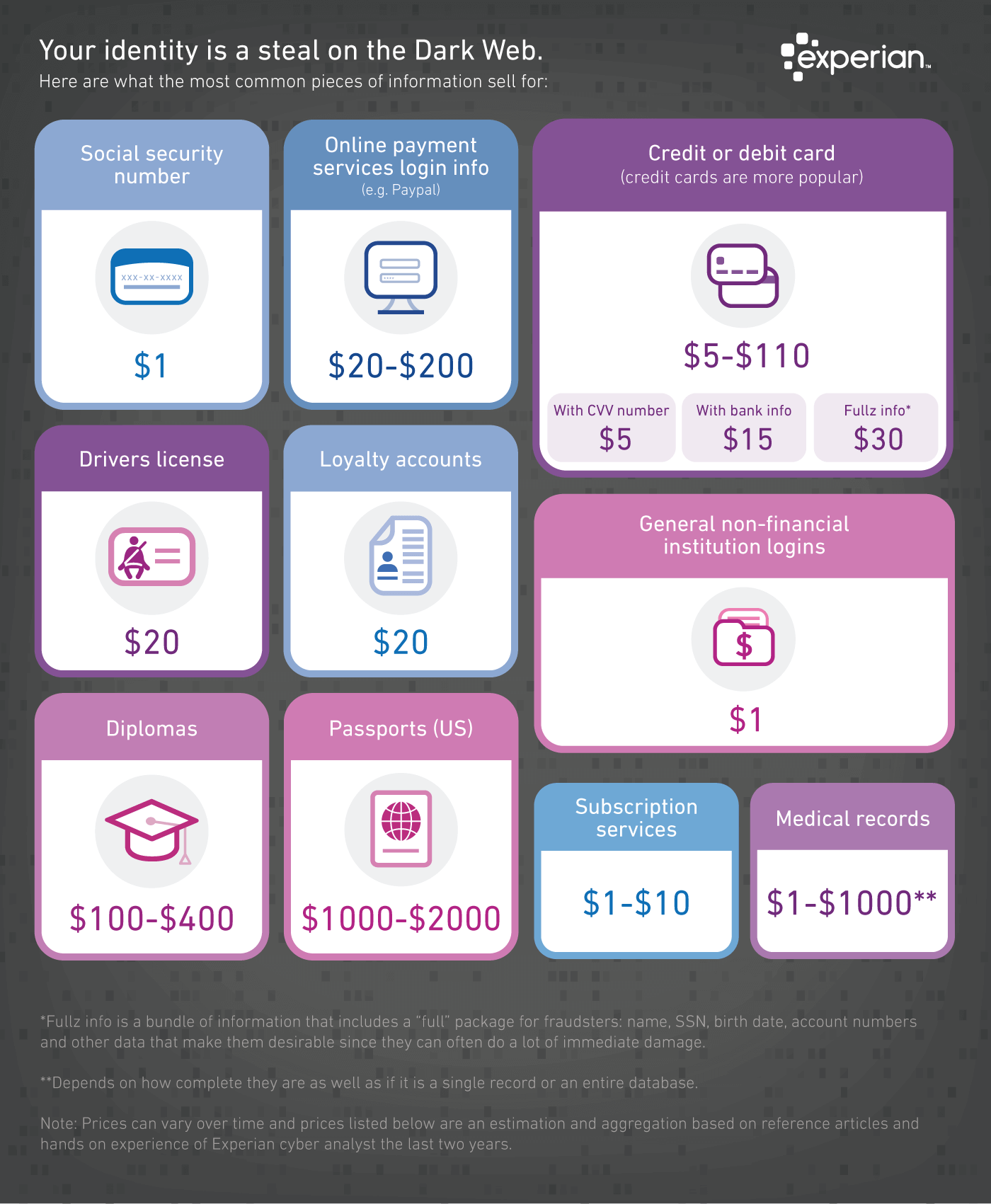
So, what's the inherent value of someone actually stealing data from a healthcare organization? The personal and professional consequences attached to each sliver of data that gets posted on the dark web. That's why, aside from credit card and social security information, medical records are some of the most sought-after records on the dark web. Well-known consumer credit reporting agency Experian recently put together an infographic detailing the typical price per record, estimating them between $1-$1000 (depending on number of records and if in bulk).
Pun aside, the hardest pill to swallow is knowing that the medical industry has actually been lagging behind other industries in terms of network preparedness, even with stringent HIPAA Compliance rules in effect.
The catch-22 of better technology and efficiency is the increased potential for cyber attacks. According to the HIPAA Journal, June 2018 alone saw 356,232 records stolen or exposed - the lowest number of records since March 2018. While these results are staggering, they're not nearly as shocking as this - roughly 2 million records have been exposed or stolen since January 2018, equaling nearly 17% of the entire US population.
So, now that we're both kind of terrified not knowing whether or not our medical information is floating out somewhere on the dark web, let's bring ourselves back to reality with some positives of the situation - much like watching an episode of Spongebob Squarepants after a horror movie.
Although these are the famous words heard in movies right before the actual worst thing happens, in this case it's actually true. Statistics show that 2015 was really the turning point year for the healthcare industry in terms of preparedness, primarily because of the notoriety of a few high-profile breaches. Security expenditures are increasing as a result, though it's questionable if they're rising at a fast-enough rate to effectively combat the rising attacks.
Which brings us to another point to consider - the reason that healthcare is so highly ranked in the industries under cyber attack list probably has less to do with the value of the records and more of the ease of penetration. Like Slater demonstrates in The Wolf, making proactive prevention on hardware access points - printers, laptops, tablets, etc. - a primary focus is a great place to start.
While not as positive at first glance, it's somewhat relieving to know that a large number of exposed records are actually just employees snooping on family, friends and acquaintances. According to Protenus, a patient data analysis AI platform used by many top health organizations, about 77% of the exposed records in Q1 2018 were a result of healthcare personnel accessing the medical records of a family member.
This is not to say that these breaches are acceptable. Physician-patient confidentiality is major part of HIPAA and the unlawful accessing of any medical records is a serious problem that can lead to an unorthodox cyber attack like social engineering as we wrote about in a previous blog post. Again, prevention comes down to the protection of records and hardware. It makes sense to evaluate some options to lock down your on-site hardware by exploring a product like Papercut or Uniflow, which both work to limit the accessibility present on your printers and copiers around the office.
While the current state of healthcare cyber security may leave a lot to desire, the reality is that the past few years have seen a renewed focus on risk management. Additionally, many of the industry's top minds are beginning to see the importance of an internal or outsourced IT department in having patients place more trust in their healthcare provider.
9 min read
Sustainability has become a top priority for businesses looking to minimize their environmental impact while maximizing efficiency. Yet, as...
6 min read
If you've recently encountered difficulties with your copier's scan-to-email feature, don’t worry — Your copier isn't malfunctioning; it's likely...

5 min read
Worried about cyberattacks hitting your business? You're not alone. Cyberattacks pose a real danger for businesses of all sizes, and without a solid...